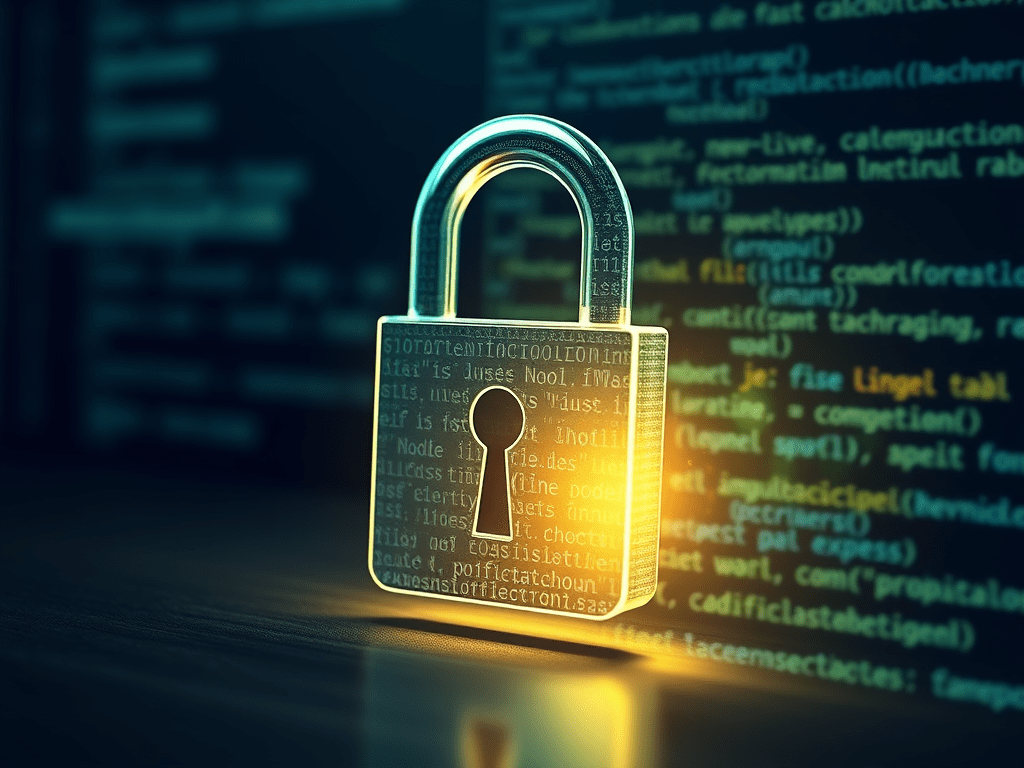
There’s a new ransomware playbook.
It doesn’t try to evade your security tools.
It just kills them.
Attackers are using BYOVD (Bring Your Own Vulnerable Driver):
- They load a legitimate, signed Windows driver
- Exploit it to get kernel-level access
- Then shut down your EDR/antivirus like any normal process
No alerts. No resistance. Just silence.
From there, encryption is trivial.
This is already being packaged into single payloads:
break in → disable security → encrypt
All in one move.
Execution time: minutes, not days.
The uncomfortable truth:
“We have EDR” is no longer a security strategy.
Attackers don’t need to bypass your defenses anymore.
They just turn them off.