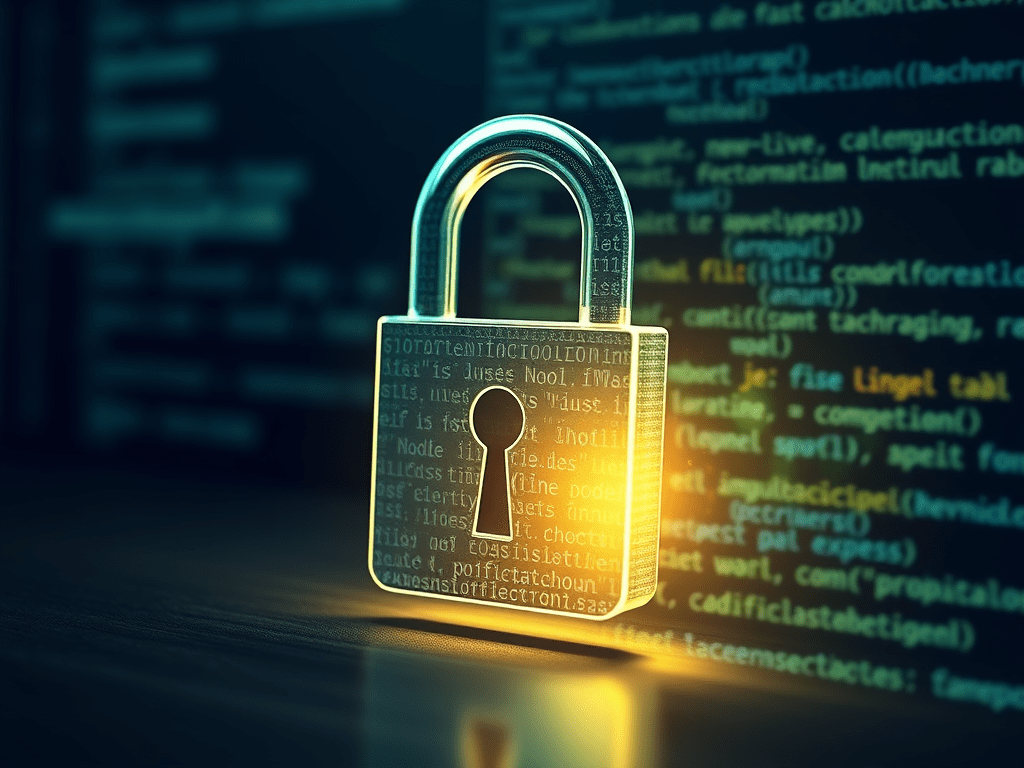
SSL/TLS certificates are essential for any web application’s security, credibility, and functionality in today’s digital landscape.
Security is the primary reason certificates matter. They encrypt all data transmitted between users’ browsers and your server, protecting sensitive information like passwords, personal data, and payment details from interception by malicious actors. Without encryption, this data travels in plain text, making it vulnerable to man-in-the-middle attacks and eavesdropping.
Trust and credibility are immediately visible to users. Browsers display clear security indicators for HTTPS sites—a padlock icon and “Secure” label—while flagging HTTP sites as “Not Secure.” This visual cue significantly impacts user confidence and can directly affect conversion rates and user engagement.
Search engine optimization benefits are substantial. Google explicitly uses HTTPS as a ranking factor, meaning certificated sites receive preferential treatment in search results. This can significantly impact your site’s visibility and organic traffic.
Browser compatibility increasingly requires certificates. Modern browsers are progressively restricting features for non-HTTPS sites, including geolocation, camera access, and push notifications. Some browsers even block mixed content or display prominent warnings for HTTP sites.
Compliance requirements often mandate encryption. Many industry standards (PCI DSS, HIPAA, GDPR) require encrypted connections when handling sensitive data. Professional applications simply cannot operate legally without proper certificates in many regulated industries.
Ok, so we got the point that’s important (=critical) – If you’re a DevOps engineer working on an AWS-based setup and need to issue SSL certificates for a domain and its subdomains — like espressolabs.com and *.espressolabs.com — this guide is for you.
In this tutorial, we’ll use:
- Let’s Encrypt for free SSL certificates
- Certbot to automate the issuance
- Route 53 for DNS-01 validation
- Ubuntu EC2 instance
- AWS Console