SMB cybersecurity is a mess. Yes – It’s 2026 and it’s broken. Big time.
Too many tools.
Too many dashboards.
Too many alerts that nobody has time—or context—to act on.
And the result?
A false sense of security.
You can have RMM, MDM, EDR, SIEM, compliance tools… and still be exposed. Not because the tools are bad—but because the system is unworkable for the people actually running it.
Most small and mid-sized businesses don’t have a SOC.
They don’t have a dedicated security team.
They don’t have time to interpret 300 alerts a day.
What they have is:
- An overstretched IT person (or MSP or the owner that is busy with 127 other things that are all urgent)
- A growing attack surface
- And a stack of tools that don’t talk to each other
That’s the real gap.
A Quick Look
We recently shared a glimpse of what we’re building here:
The Problem Isn’t Detection. It’s Execution.
The industry has optimized for finding problems.
But detection without action is just noise.
If a phishing attempt is detected but not quarantined fast enough, it’s a failure.
If MFA isn’t enforced consistently, it doesn’t matter that you know about it.
If remediation requires five tools and manual coordination, it simply won’t happen reliably.
Security, at the SMB level, doesn’t break because of lack of data.
It breaks because nothing actually gets done.
What We’re Building at Espresso Labs
We started with a simple question:
What if security didn’t just alert you—but actually handled the problem?
That led us to rethink the model entirely.
Not another dashboard.
Not another stream of alerts.
Not another “single pane of glass” that still requires human glue.
Instead, we’re building something closer to an operator.
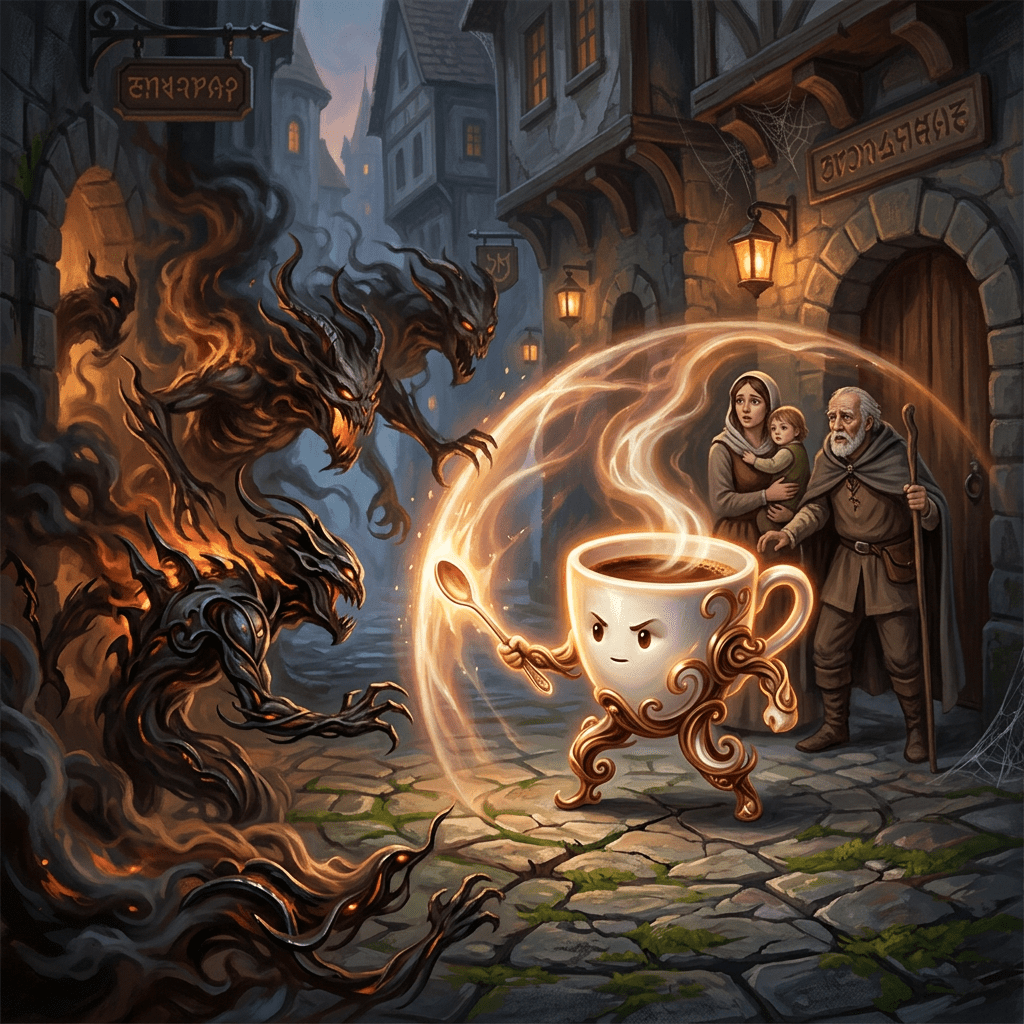
☕ Meet the AI Barista
We call it the AI Barista—not because it sounds nice, but because it reflects the job:
You don’t go to a barista for raw ingredients.
You go because they take complexity and turn it into something finished.
That’s exactly the role here.
The AI Barista doesn’t just observe—it acts:
- Quarantines threats automatically
No ticket.
No delay.
No “we’ll get to it.” - Verifies MFA enforcement continuously
Not as a policy, but as a living control. - Guides and executes remediation
Without requiring a full SOC or deep security expertise
This isn’t about replacing humans.
It’s about removing the parts humans are consistently bad at: speed, consistency, and follow-through.
Killing the Tool Sprawl
Underneath, there’s another important shift.
Today’s SMB stack is fragmented by design:
- RMM for device management
- MDM for mobile
- EDR for endpoint security
- Plus whatever you bolt on for compliance
Each layer adds cost, complexity, and integration pain.
We’re collapsing that into a unified platform—not for the sake of elegance, but because fragmentation is the root cause of inaction.
When systems don’t talk, people become the integration layer.
And people are the least reliable part of any security system.
The Real Goal
This isn’t about building a cooler security product.
It’s about changing the outcome.
Giving SMBs:
- Enterprise-grade protection
- Without enterprise overhead
- Without needing a security team to operate it
Because the truth is simple:
Most small companies don’t need more tools.
They need fewer tools that actually work—and actually do the job.
Where This Is Going
We’re still early—but the direction is clear.
Security is moving from:
- Tools → Systems
- Systems → Automation
- Automation → Agents that operate on your behalf
The winners won’t be the companies that detect the most threats.
They’ll be the ones that resolve them—fast, reliably, and without human bottlenecks.
That’s the bar.
And that’s what we’re building.
Discover more from Ido Green
Subscribe to get the latest posts sent to your email.