A founder asked me recently a simple question:
“How many security tools do we actually need to be protected like an enterprise?”
I gave him the honest answer.
Six to ten different platforms. Minimum.
There was a pause.
Then his face dropped.
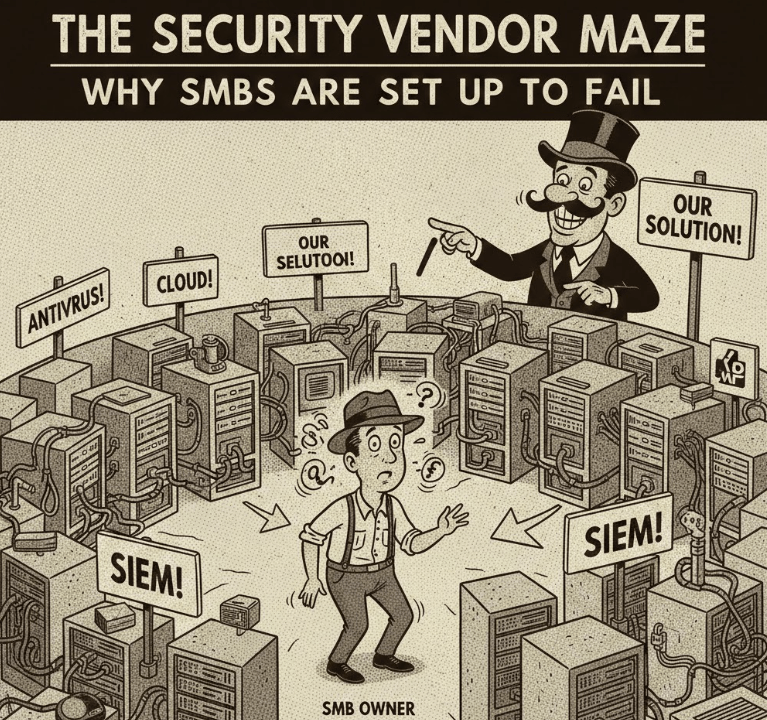
Because in that moment, he realized what many SMB founders eventually discover the hard way: modern cybersecurity was never designed for companies like theirs.
What “Enterprise-Level Security” Actually Means
When people say “enterprise-grade security,” they usually imagine something vague and reassuring.
In reality, it’s very concrete—and very fragmented.
To get reasonable coverage today, you typically need:
- Identity & Access Management (IAM)
SSO, MFA, conditional access, least privilege - Endpoint Protection / EDR
Malware detection, ransomware prevention, behavioral analysis - Email Security
Phishing protection, attachment scanning, impersonation detection - Network Monitoring
Firewalls, intrusion detection, anomaly detection - Backup & Disaster Recovery
Immutable backups, ransomware recovery, business continuity - Compliance & Audit Tooling
Logging, reporting, policy enforcement, evidence collection
And that’s the baseline.
If you want to do this “right,” you’ll probably add vulnerability management, device management, and cloud posture management on top.
Here’s the catch:
Each one usually comes from a different vendor.
- Different dashboards.
- Different pricing models.
- Different alerting systems.
- Different renewal cycles.
- Different support teams.
Enterprises Can Absorb This.
SMBs Cannot.
In a large enterprise, this mess is survivable because there’s an entire organization built around it:
- A security team to tune alerts
- IT admins to onboard/offboard users
- Procurement to manage vendors
- Budget to tolerate inefficiency
In a 30-person company?
The “IT department” is often:
- The CEO / COO / office manager
- A part-time MSP
- Or a founder who “knows computers”
That person is expected to:
- Compare vendors
- Configure policies
- Respond to alerts
- Keep everything up to date
- Explain incidents to leadership
All while doing their actual job.
This is not a skills problem.
It’s a systems design failure.
The Coping Strategy: Pick Two Tools and Hope
What actually happens in most SMBs is painfully predictable.
They buy:
- An endpoint tool
- Maybe email security
Then they stop.
Not because they don’t care about security.
Not because they’re reckless.
But because:
- The complexity curve is brutal
- The mental overhead is exhausting
- The marginal benefit is unclear and they wish ‘just’ do to their job not worry about some ‘threats’ they don’t know about.
So they cross their fingers and move on.
Hope becomes the security strategy.
“But We’re Too Small to Be a Target”… Right?
This is where the story usually breaks.
According to multiple industry reports, around 43% of cyberattacks target small businesses.
Why?
Because attackers are rational:
- SMBs have weaker defenses
- Fewer detections
- Slower response
- Smaller blast radius, but higher success rates
Attackers don’t need sophistication.
They need scale.
One compromised SMB is manageable.
A thousand compromised SMBs is a business model.
The Uncomfortable Truth About the Security Industry
Here’s the part we don’t say out loud often enough:
The security industry built for enterprises first.
SMBs got whatever could be resized, repackaged, or discounted.
That’s why SMB “solutions” often look like:
- Enterprise tools with features disabled
- Bundles of point solutions glued together
- Interfaces that assume security expertise
But the result is the same:
SMBs are asked to operate systems designed for a completely different reality.
What SMBs Actually Need
SMBs don’t need:
- 12 dashboards
- 400 configuration toggles
- Weekly alert storms
They need:
- Coverage without orchestration hell
- Sensible defaults
- Opinionated security
- Clear signals instead of noise
- Protection that assumes no dedicated security team
In other words:
Security that matches how SMBs actually operate.
Not watered-down enterprise tooling.
Not duct-taped point solutions.
Something purpose-built.
This Is the Problem We’re Trying to Fix
When we started building our solution, we weren’t trying to invent new security primitives.
We were trying to answer a simpler question:
What would security look like if it were designed from day one for a 10–100 person company?
- One platform.
- Unified visibility.
- Automated decisions.
- Minimal human babysitting.
Because founders should spend their time:
- Growing the business
- Serving customers
- Building products
Not learning how five vendors interpret the word “incident.”
Final Thought
If you’re an SMB founder or operator and this sounds familiar, you’re not alone.
You’re not negligent.
You’re not behind.
You’re operating inside a system that wasn’t built for you.
SMBs deserve security that respects their constraints, not punishes them for lacking enterprise resources.
If you’re tired of choosing between comprehensive security and actually running your business, let’s talk or just join our waiting list at: https://espressolabs.com/
Discover more from Ido Green
Subscribe to get the latest posts sent to your email.